The security team is focused on what matters, and cloud adoption is skyrocketing.
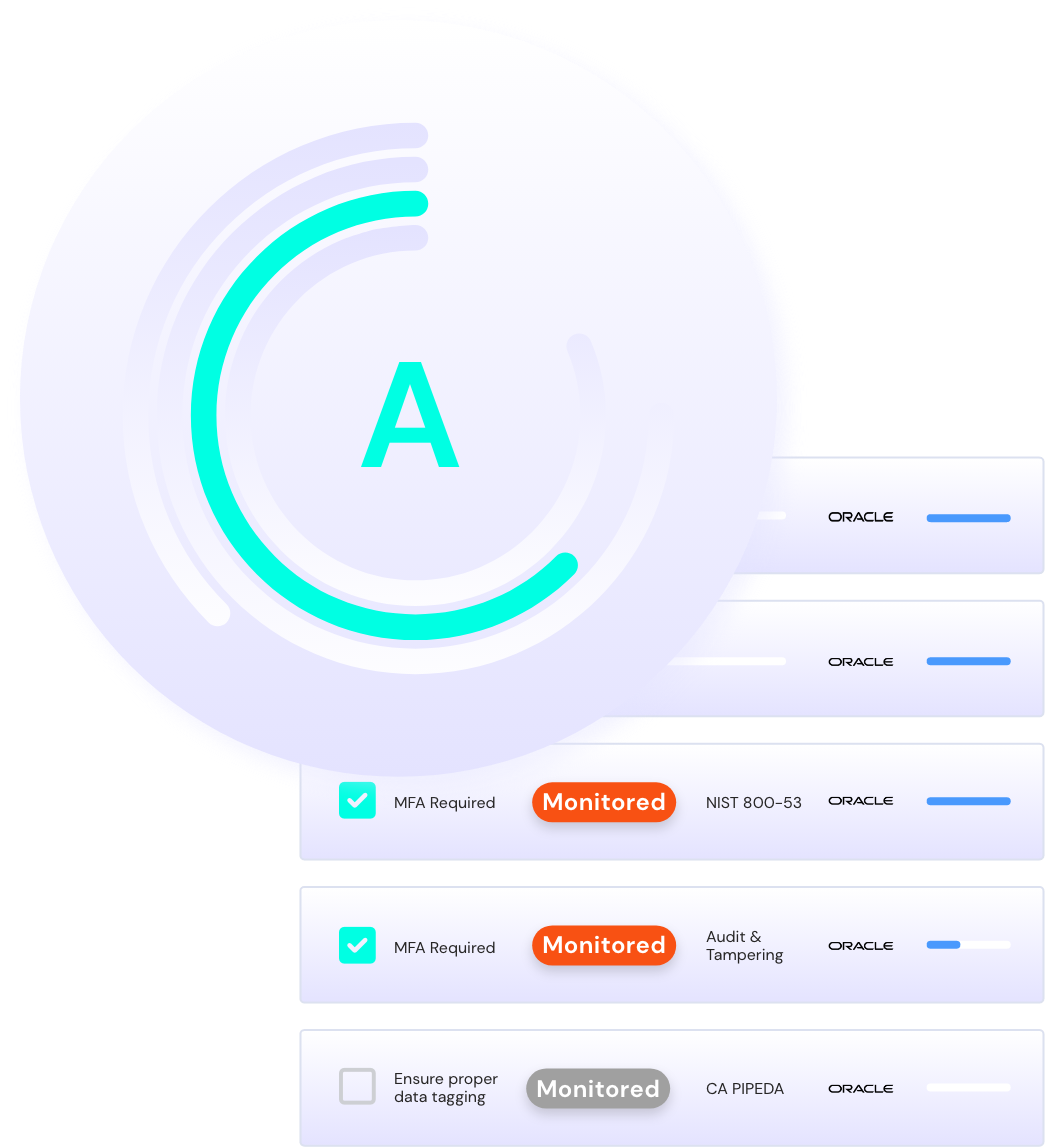
A set of simplified controls within a tailor-made framework made secure, automated deployment easier – and since Sonrai automatically keeps pace with the cloud provider’s innovation, maintenance of policies is minimal. Since automation unlocks an anomaly-centric alert model, there are far fewer controls than an average large financial enterprise – meaning less alerts, less false positives, and more time on threat investigation.
More importantly, the security team has made a far-ranging impact on the business. The dev team doesn’t waste valuable resources on managing cloud deployment. A data-centric approach means customer data exposure risk is minimized. And they’ve enabled the cloud team to meet the CIO’s mandate for better customer experience – with predictable, scalable, secure deployment, workloads are hitting the cloud faster, and cloud adoption is skyrocketing.