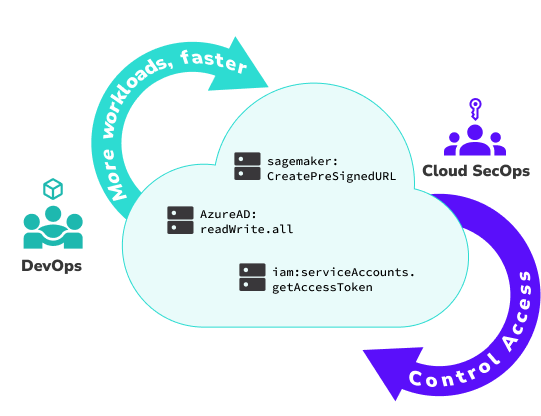
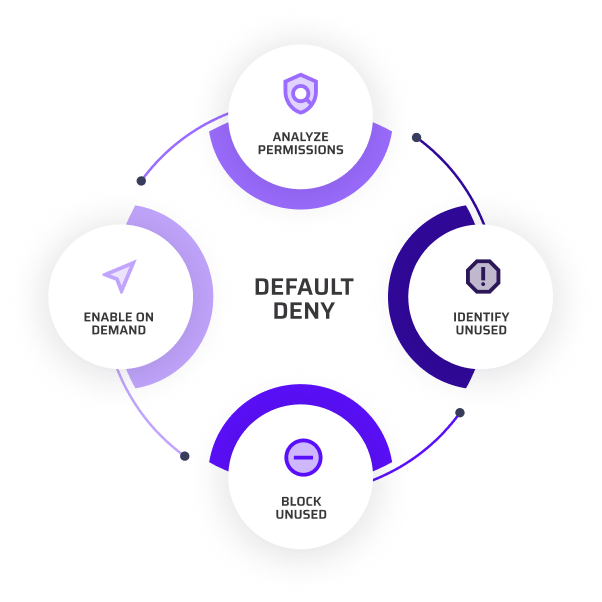
Least privilege is the gold standard for managing identities and reducing risk, but pulling it off at cloud scale is hard. There are 42,000+ possible permissions, so let’s focus on protecting just the most privileged ones.
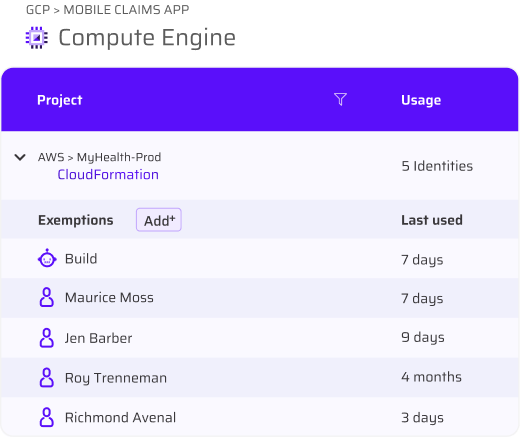
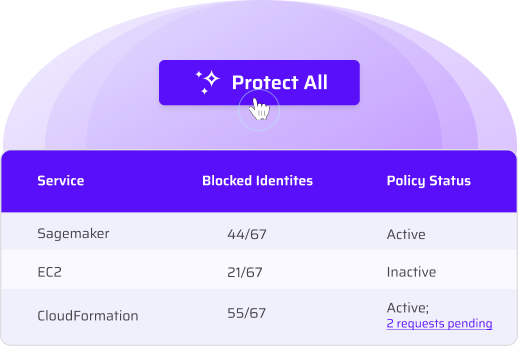
This least privilege solution enforces security by restricting unused privileged permissions from every human and machine identity not using them — all in one automatically managed global policy.