Frequently Asked Questions
Cloud environments rely heavily on dynamic identities and over-permissive roles, which makes privileged access one of the top causes of breaches. Cloud PAM reduces risk by ensuring only the right identities have the minimum privileges they need, only when they need them.
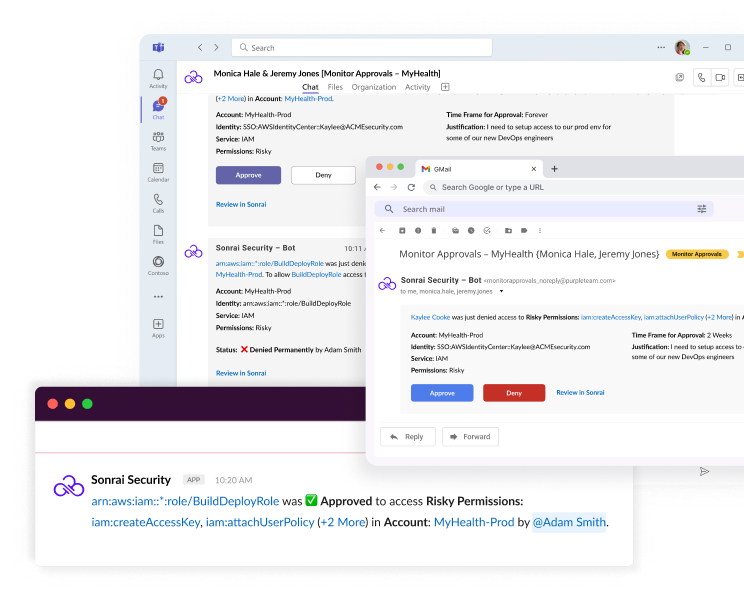
Traditional PAM focuses on static credentials and vaults, while Sonrai Security is built natively for the cloud and manages permissions across identities, roles, and AI agents. Sonrai provides visibility and control without jump boxes, password vaults, or disruptive workflow changes.
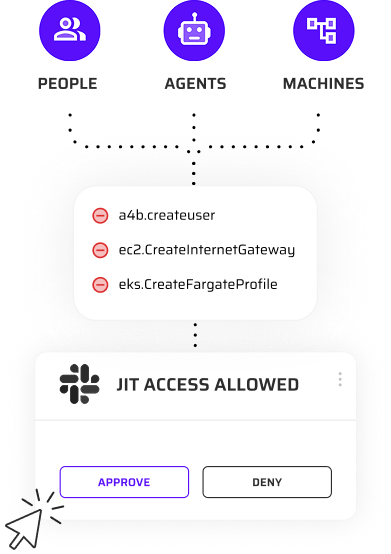
Yes, Sonrai Security governs both human users and non-human identities such as roles, service accounts, and workloads. This unified approach is critical in cloud environments where machine identities often outnumber humans.
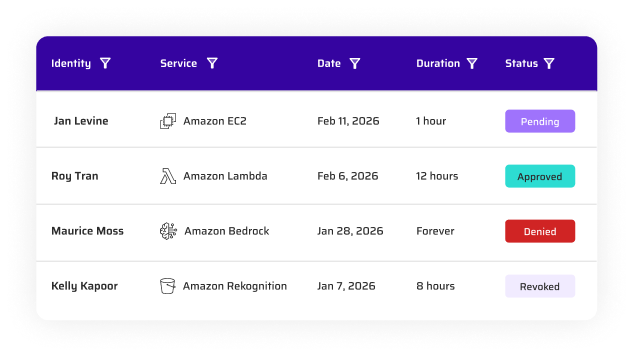
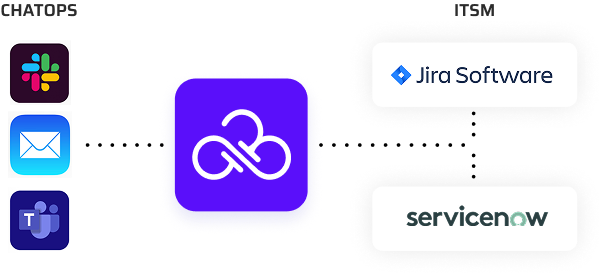
Sonrai operates out-of-band using cloud APIs, continuously analyzing and validating permission usage before changes are enforced. Any identity using privileged permissions maintains use of that permission. This approach avoids inline controls that could disrupt running applications.
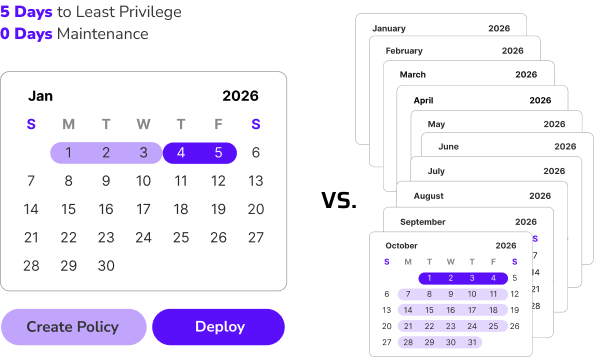
No, Sonrai reduces risk without introducing downtime by identifying safe, least-privilege changes and validating impact before remediation. Access adjustments are made carefully to preserve application functionality.
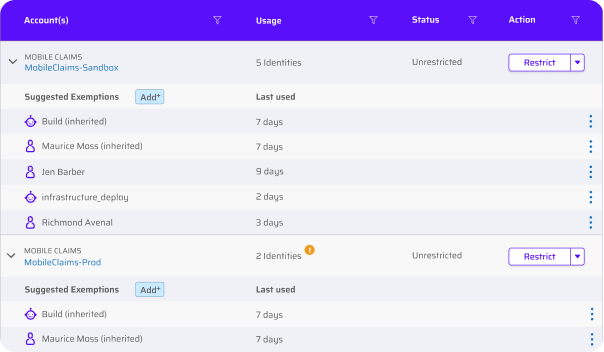
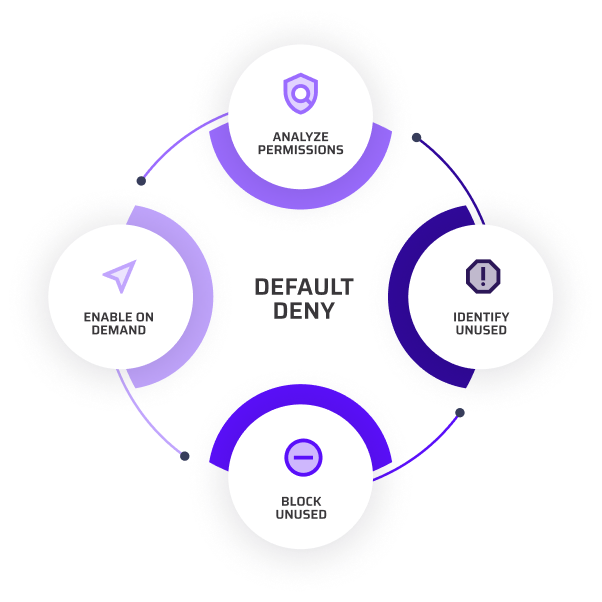
Sonrai uses continuous discovery, graph-based analysis, and policy-driven automation to identify excessive privileges and remediate them at scale. This allows teams to enforce least privilege automatically across complex cloud environments. Quickly and at scale.