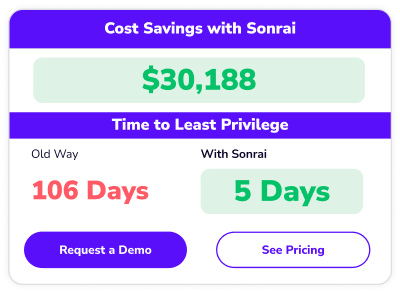
ROI of The Sonrai Cloud Permissions Firewall
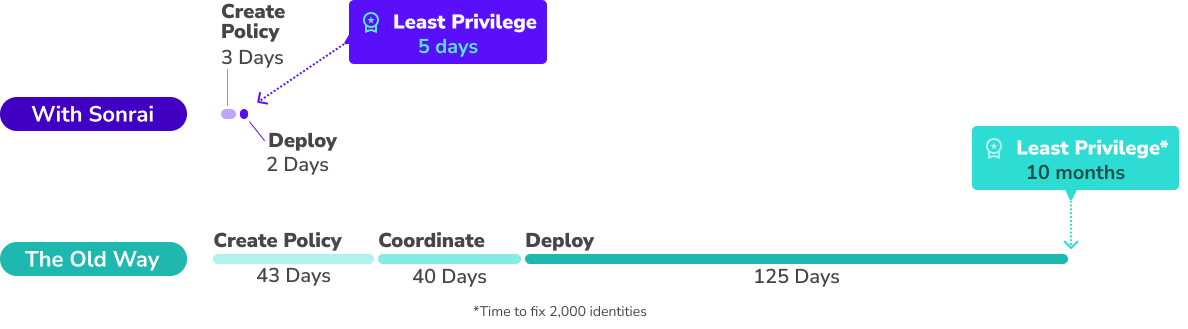
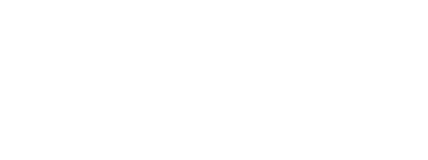
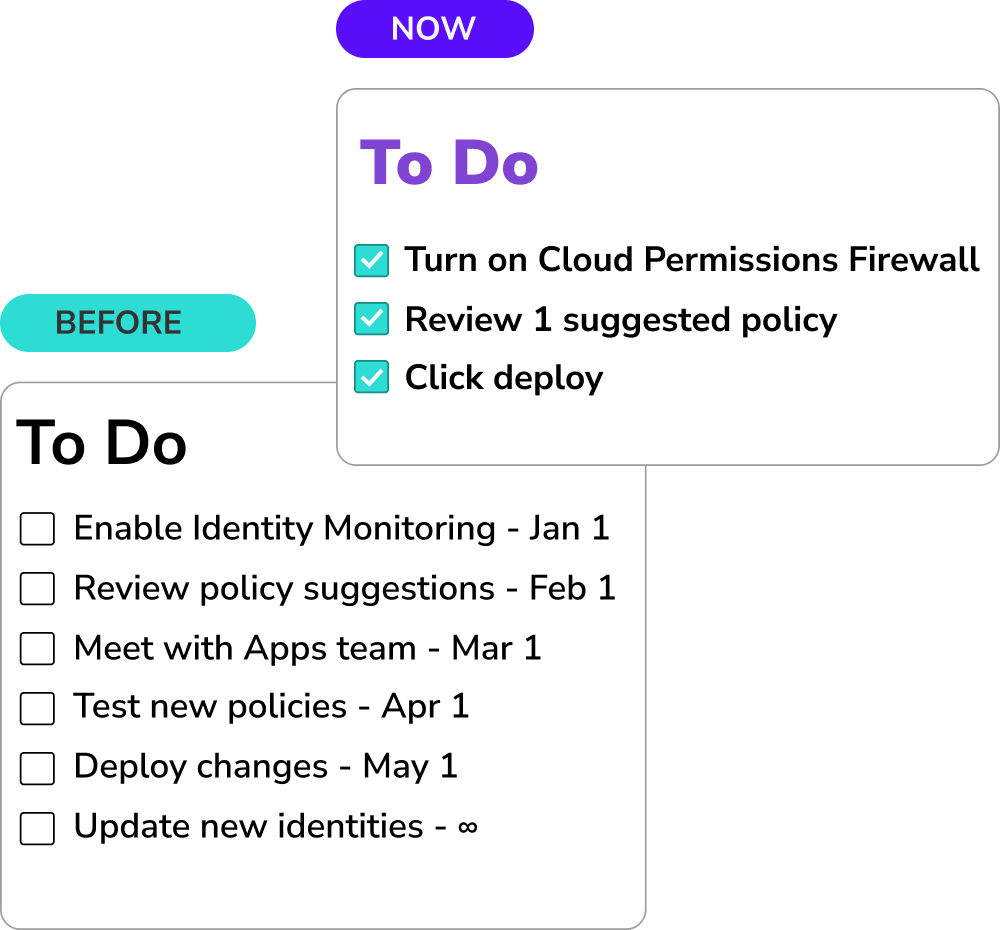
Historically, implementing security controls has meant more work on your teams, money on the table, and a lot of time spent. And what’s it got you?
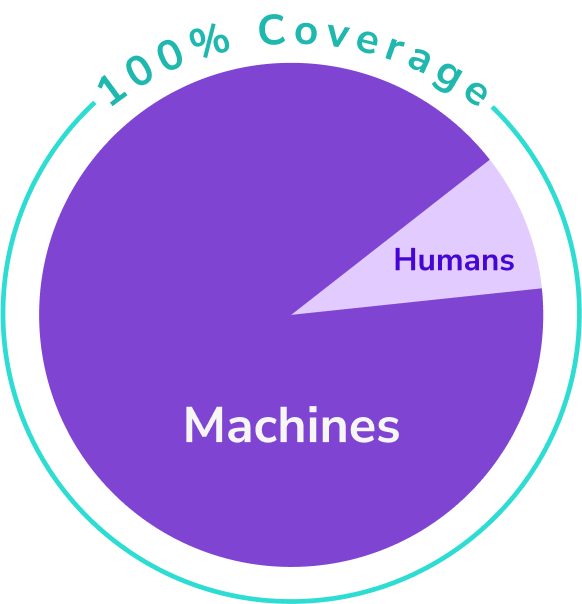
A fraction of your identities secured? A ‘good start’? We built a solution that cuts attack surface risk instantly with the click of a button without the added burden on your resources.
With the Cloud Permissions Firewall there are no sacrifices, just good security with less work and quicker timelines – talk about saving money.