Cloud Misconfiguration
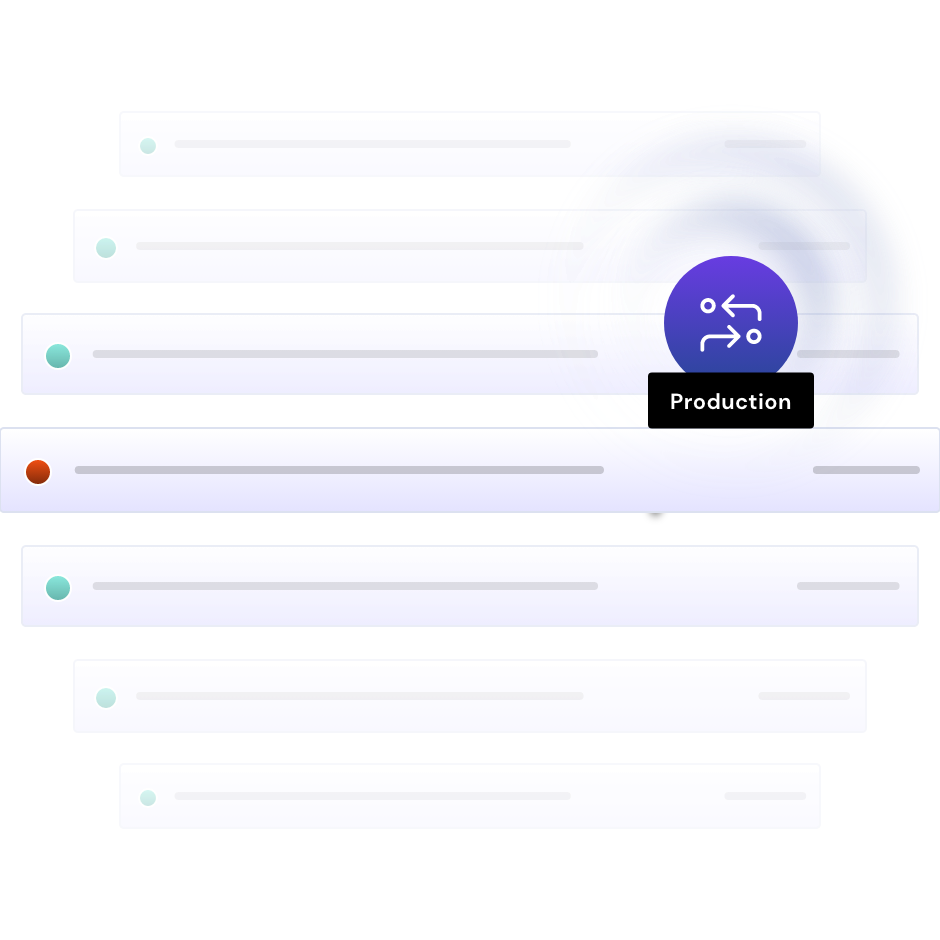
Avoid misconfigurations with vigilant monitoring and automatic policy application
Misconfigurations remain the most famous and frequent path to data breach.
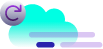
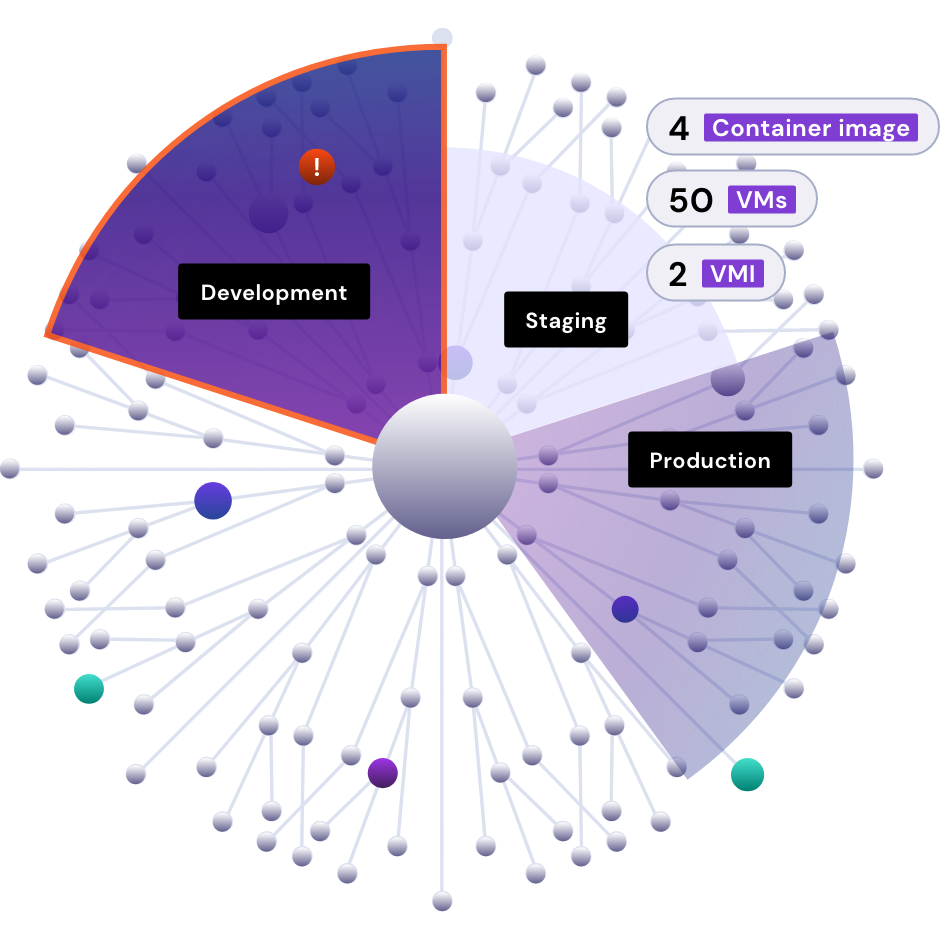
Despite cloud providers’ great efforts to help customers solve this problem, exposing datastores to the internet still beguiles cloud security teams, regardless of their maturity. The dynamism and complexity of cloud development keeps opening the door to misconfiguration. Getting past this problem means seeing everything in your cloud, continuously monitoring, and applying the right policies automatically.