Sonrai cloud security platform, products and services are covered by U.S. Patent Nos. 10,728,307 and 11,134,085, together with other domestic and international patents pending. All rights reserved.
Comparing Cloud Identity Security Capabilities
| Feature |  |  |
|---|---|---|
| Public Cloud Environments | Amazon Web Services (AWS), Microsoft Azure, Google Cloud Platform, Oracle Cloud Infrastructure | Amazon Web Services (AWS), Microsoft Azure, Google Cloud Platform, Oracle Cloud Infrastructure |
| Identity, Access and Permissions Visibility | More than 40,000 permissions analyzed including boundary conditions and nested groups | Directly attached permissions |
| Identification of Identity Cloud Risks | Overprivileged identities, privilege escalation (e.g. sandbox to prod), cross-account and cross-cloud access. | Overprivileged identities |
| Detection of Threats | Detection of unusual access, change in permissions & potential access, unusual behavior and changes in risky configurations | Unusual identity activity based on pattern matching from activity history |
| Remediation Automation | Automated prevention and remediation bots, escalations, CLI and console instructions | CLI and console instructions |
| Centralized Platform | One integrated platform with tools for security platform configuration, workloads, data and identities | A multi-product solution with separate tools for platform configuration, vulnerabilities and identities lacking a unified view of cloud risk |
| Deployment | Agentless, read-only access deployment | Agents required for full visibility and risk analysis |
See Sonrai In Action
Check out our interactive tour to see how security leaders secure their cloud, manage identities, and protect their data with Sonrai.
What security leaders say about Sonrai
“Sonrai is one of the leaders in this space, both from a product maturity perspective, and the thought leadership.”
Director of IT, Banking Industry
Source: Gartner Peer Reviews

“Sonrai offers full visibility into effective permissions and the identity chain – giving my team value insight to identify, root cause and remediate identity risks.”
Enterprise Customer
Source: G2

See How Sonrai Compares to
Palo Alto Prisma
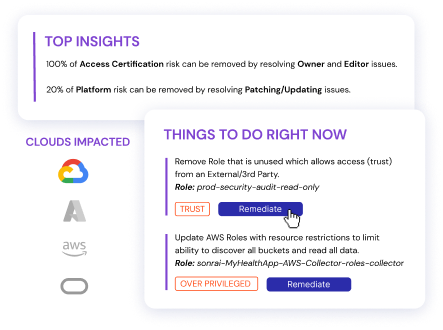
See the Sonrai technology in action with a comprehensive view of where your cloud identity
risks are - delivered in just 24 hours. This comprehensive report includes specific next steps
and is a valuable opportunity to compare findings from other solutions.