Table of Contents

Share this entry
In an age of high-profile security breaches, cybersecurity remains an all-hands-on-deck initiative for today’s smartest businesses. As the recent cyberattacks against the U.S. Treasury and Commerce Department demonstrated, no organization is safe from cybercrime. Constant vigilance is required to prevent malicious attacks from impacting operations.
Strong cybersecurity starts and ends with the ability to detect threats. Unfortunately, this can be extremely difficult due to an increasingly prevalent problem called alert fatigue.
What is Alert Fatigue?
When you think of a security alert, the first thing that comes to mind is likely an external attack from an unknown party. Yet an alert can occur for any number of reasons, with varying levels of severity. For example, an alert may be triggered by a dormant admin account that is enabled but not in use. Or it could stem from a permissions change, an exposed data store, or a shared account that should be private. The list goes on and on.
Because the number of alerts is so extensive in today’s digital age, it can be challenging for teams to organize and manage them at scale. There is simply no way to manually monitor and address every incoming alert across an enterprise with any sense of urgency or any sense of thoroughness.
Alert fatigue occurs when security teams and engineers become desensitized to security threats because there are too many to keep up with. Instead of blocking these threats, they allow them to pass through undetected into an organization. This can damage the safety and stability of a company, undermining defenses and putting networks, data, apps, and cloud environments all at risk.
Alert Fatigue Harms Enterprises
Here are some of the main ways alert fatigue adversely impacts organizations.
Missed Alerts
A large volume of false positives can make it difficult for your team to differentiate between minor alerts and severe ones. As a result, critical alerts can slip through undetected, leading to serious consequences.
According to one survey, C-level security executives at large enterprises receive more than 10,000 alerts each month. Of these, 52 percent are false positives and 64 percent are redundant. When you know that many of the alerts aren’t helpful, it’s that much harder to pay attention to them.
High Turnover
Working in security can be very stressful due to around-the-clock notifications, 3 a.m. wake-up calls from PagerDuty, and full inboxes. Alert fatigue can reduce productivity and accelerate employee turnover, increasing costs while making it harder for companies to combat threats.
A False Sense of Security
When issues are undetected, it can lead to a false sense of security within an organization. Security teams may think they are keeping the company safe from cybercriminals when in fact there are gaping holes in their defenses. Since the average cost of a data breach is $3.86 million, this is a big deal.
Tips for Preventing Alert Fatigue in Your Organization
As you can see, alert fatigue can lead to catastrophic consequences. As such, businesses need to establish strong security frameworks to push back against alert fatigue and make it easier for security teams to recognize and combat incoming threats.
With that in mind, let’s take a look at some of the ways you can prevent alert fatigue.
Prioritize Alerts
Combat alert fatigue by making it easy for security teams to visualize and prioritize incoming alerts so that security professionals don’t have to question what to focus on when responding to them. Companies should classify threats based on different tiers to best determine the level of danger they pose
For example, discovering ransomware or an unauthorized intruder on a network may be more urgent than responding to a suspicious permission change.
Consolidate Security Tools
DevOps professionals often have to use multiple systems and tools when responding to alerts. This issue can increase response and resolution times while creating pointless backend work. Teams can reduce this by leveraging dashboards that consolidate alerts in one place, giving your team a single source of truth.
Establish a Layered Defense
It’s not realistic to try and prevent all incoming attacks. Security teams need to come to terms with the fact that some threats will inadvertently slip through the cracks and make their way into the organization.
Companies need to establish a layered and automated security strategy that extends from the edge of the network to the human layer, with multiple systems working together to detect and eliminate threats.
Leverage DevOps for Security Monitoring
In the past, centralized security teams were solely responsible for threat monitoring. Today, DevOps is playing an increasing role in security management by covering the whole stack.
By shifting security to DevOps, teams can combine security and agility — expediting response times while pushing back against alert fatigue.
Make Alert Fatigue a Priority
The key to fighting alert fatigue is to avoid becoming complacent. Companies need to constantly analyze systems and processes to figure out what’s working and where threats are being overlooked due to a lack of oversight.
For the best results, security teams should make it a regular point to review what’s working and what isn’t and determine the better way forward.
Leveraging Sonrai to Combat Alert Fatigue
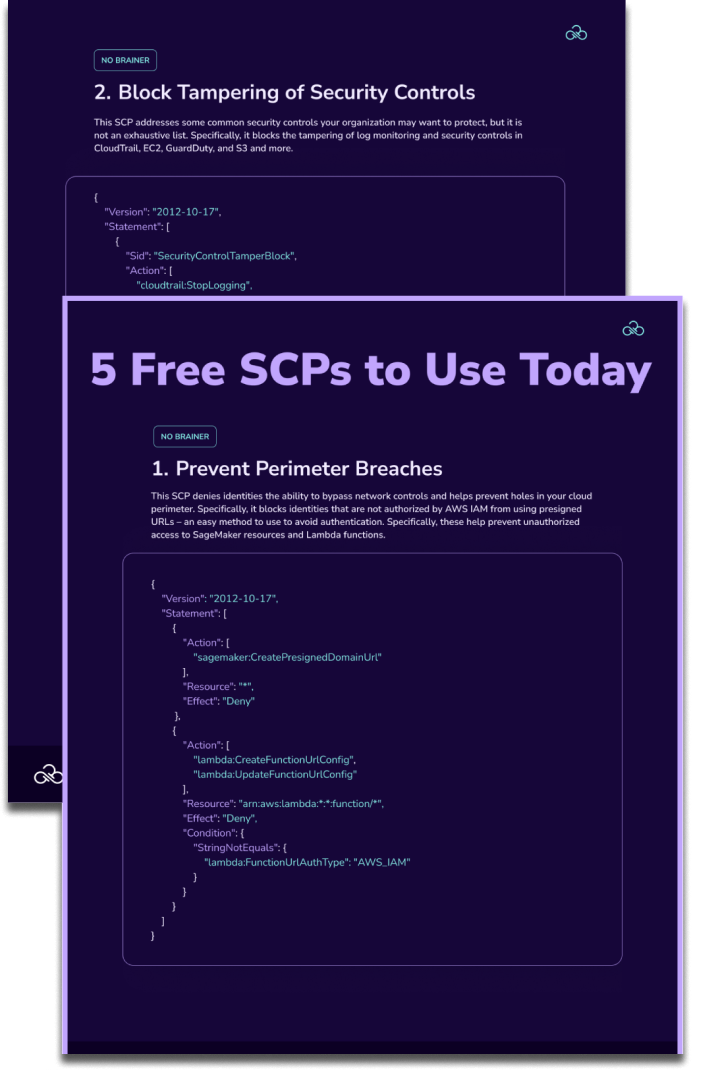
Cloud Security and CloudOps teams end up with hundreds of alerts that are not appropriate for the environments monitored causing complaints of too many false positives by the teams responsible. Sonrai’s public cloud security platform organizes all analyses, alerts, and actions for environments into “swimlanes” and directs relevant issues to the proper owners or creates an automated process responsible for remediating the issue.
The platform’s swimlanes give each environment uniqueness and importance with a single pane of glass with a visual representation of cloud security posture and overall risk. This means policy configuration issues in a development CI/CD pipeline are reported to workload owners and not security teams to be addressed before infrastructure and code is promoted to production. Our Security Center further breaks down information by Control Framework allowing easy separation by issues such as incidents, over-privileged identities, network misconfiguration, encryption lifecycle, and data exposure issues. This allows teams responsible for a particular swimlane to prioritize alerts. It also allows a top-level view of all workloads to evaluate if they have unique or systematic issues that exist across all workloads in the organization.
With Sonrai Dig, companies can access strong governance automation and end-to-end security over a flexible, cloud-based platform. Request a demo of Sonrai Dig today to learn more about what you can do to protect your team from alert fatigue and build a more secure cloud environment.
THE ARCHITECT
The Newsletter for Cloud Security Leaders. 1x a month.
Read the latest news and insights
Sonrai cloud security platform, products and services are covered by U.S. Patent Nos. 10,728,307 and 11,134,085, together with other domestic and international patents pending. All rights reserved.