Table of Contents

Share this entry

Once upon a time, our organizations were reliant on on-prem data centers where things were mostly static from a resource perspective. Vulnerability management was a large priority and entirely necessary for finding and patching exploitable holes in your servers and endpoints.
Scanning for vulnerabilities is still important, but the medium in which businesses operate today is entirely different. With the transformations of our technology from on-prem to the cloud, the methods in which we protect them must transform too. The old concepts of traditional security do not always apply to the cloud, instead they must be molded to fit contemporary environments and needs. If the tools and processes designed to run on-prem are just simply transferred to the cloud, your organization will quickly find it is expensive and inefficient to secure, and might also lead to blind spots. Certain tools created for on-prem environments were not designed to be deployed in the ephemeral space of the cloud.
So What is CWPP?
According to Gartner, CWPP, Cloud Workload Protection Platform, is a “workload-centric security solution that targets the unique protection requirements” of the workloads operating in today’s cloud. For many organizations, it’s vulnerability scanning for their cloud. Any workload performing a service, be it AWS EC2, Azure Virtual Machines, or Google containers, offers an opportunity for attack, no matter how briefly they are spun up. CWPP offers protection for workloads at any point in transit.
As cloud native applications continue to expand across cloud resources, unique security needs arise for each individual workload. The shift to microservices has led to an explosion of entities to protect.
Environments are also evolving quickly today. Often DevOps teams are deploying on a daily or weekly basis, meaning your cloud environment is changing frequently, making visibility difficult for security teams.
This all calls for CWPP solutions.
Why is CWPP Important?
Protection over all things within a workload is needed – the application itself, any data produced or entering the workload and any interaction between the application and the identity using it. Today, securing workloads is an extremely complex task as organizations are working in any combination of on-prem machines to public clouds to private ones. Protecting workloads is critical, as they often host and have access to your organization’s most sensitive asset — data. Securing your workloads is securing your data.

Vulnerability Management
Organizations are relying more and more on cloud-based applications and development time is often pressed to meet business demands. This leads vulnerability management to be one of the greatest concerns Cloud Engineers, DevOps, and Security Teams are facing when it comes to workload protection. Teams want to meet deadline frameworks, without leaving exploitable entryways into your environment. Teams need a way to detect vulnerabilities and patch them before it’s too late. But there’s more to the vulnerability management story: the need for risk in context.
Read more about vulnerability management in the cloud.
Workload Context
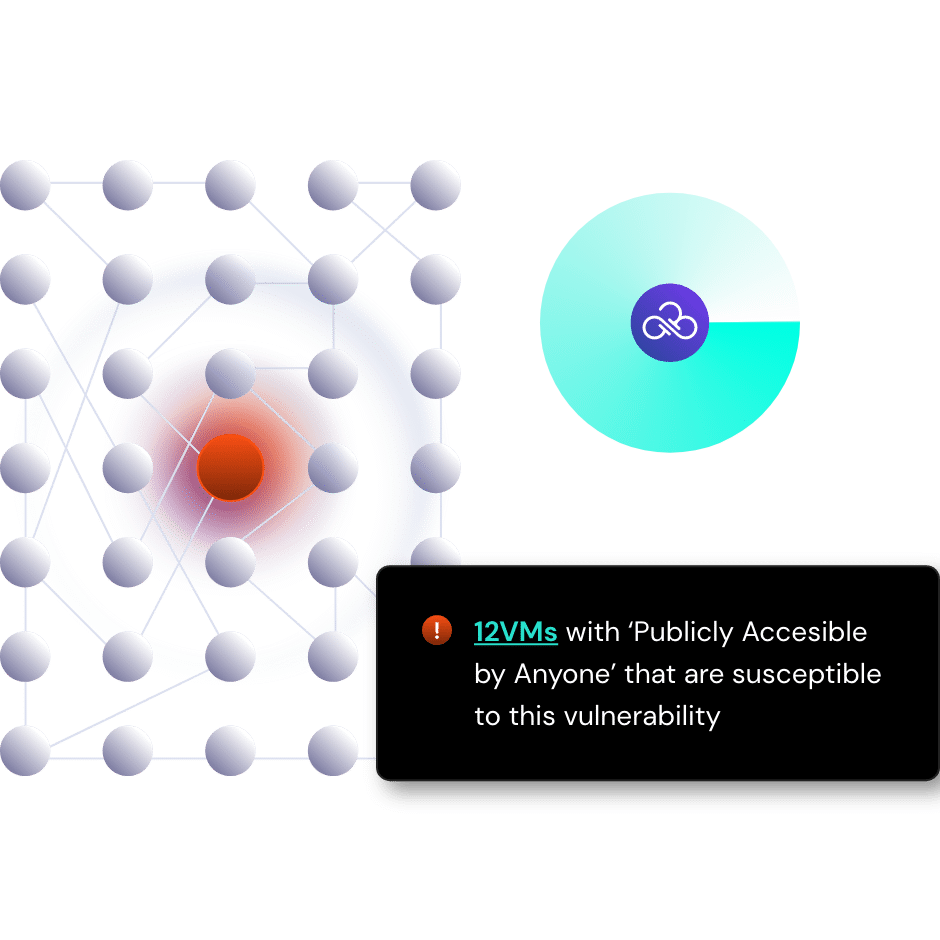
With an entire environment to manage, it is easy to feel overwhelmed by resource and tool sprawl. Cloud Workload Protection Platforms offer context, enabling a more complete picture of your workload vulnerabilities, allowing you to prioritize concerns that pose the greatest potential risk.
The importance of workload protection solutions only increases when you consider other areas of cloud security like identity, data and platform. With context, a workload with a moderately rated vulnerability can quickly become a critical risk if that workload is exposed to the internet, has a grossly over permissioned Identity and access to your most sensitive data. Having this insight allows your team to raise this concern to the highest priority.
Traditional CWPP vendors rank their vulnerabilities based on a raw CVSS score, but more modern workload protection can provide this critical context. When teams are already extremely overwhelmed with alerts and risks, having this context also helps you know where you can de-prioritize and focus elsewhere. Consider a workload that is 4 layers deep in your cloud, is at least privilege and has no access to any data, then perhaps this gets downgraded to something that can be addressed at a later date.
How Does CWPP Work?
A cloud workload protection platform will discover all of the workloads existing within your cloud environment and then evaluate them for potential security vulnerabilities. This is achieved all without the need to install an agent or give the scanner highly permissive access to the resource. Discovering potential vulnerabilities is just the first step, a mature CWPP will then have the ability to assess the risk in context and offer the ability to implement security controls to fix these issues, not just in one cloud, but across all of your clouds, from a single place. For any known or common security threats, a platform will also provide protection for your cloud workloads, for some, this includes runtime protection, malware detection and remediation or network segmentation.
What are the Benefits of Using CWPP?
Centralized Information
A CWPP will provide a single pane of glass to show what is happening in every workload not only within one cloud but across all your cloud environments.
Context
If you find the right workload protection solution, one that integrates with other cloud security solutions like posture management and identity management, CWPP tools can provide your team critical context. This context is what helps clarify whether a vulnerability is a pressing need (e.g. a VM that has access to sensitive data and is exposed to the internet) or something that can wait till the next day.
Visibility
Insight into each individual workload is exceptionally important and allows teams to better manage vulnerabilities not just in one cloud at a time, but across all clouds. Taking it a step further, visibility adds context which means that the true issues rise to the top, so that your teams are always focused on the true most important risks.
Workload Activity Monitoring
This detects any anomalies that deviate from the policies you have in place indicating a potential threat. Once this is done it will alert the necessary teams.
Faster Resolutions
Elevated CWPP solutions will provide your team prioritization of vulnerabilities through ‘risks amplifiers’ and offer intelligent workflows to send concerns to the correct team, all working to expedite remediation. Coupled with this is automation, to ensure that your risks are addressed at the speed and the scale of the cloud.
Operationalized Workflow
By consolidating workload concerns into a centralized view and providing alerts when a vulnerability presents itself results in faster resolutions and security at the speed and scale of the cloud, less stress, the ability for employees to focus on more pressing matters and therefore a happier SecOps team.
How To Choose a Cloud Workload Protection Platform
Here’s a few things to consider or ask a vendor when selecting a CWPP:
- Is there insight into how the workloads connect to sensitive data or privileges?
- Is there built-in prioritization of workload risks with the greatest blast radius?
- Does the solution offer agentless scanning to avoid disruption?
- Can the solution integrate with your existing workflows or scanners?
- Are findings specific to the host?
Try Cloud Workload Security Today
The cloud and its services have allowed organization’s to grow exponentially and complete tasks in seconds that could have taken hours previously. No matter how briefly your workload is spun up, you need a reliable way to scan for vulnerabilities and prioritize risks, especially the ones that you didn’t know you had.
Teams are inundated with alerts as the scale of the cloud only increases. Scanning for vulnerabilities is just the beginning. Sonrai’s Workload Security (CWPP capability) provides a full-picture of context upon discovering cloud vulnerabilities you didn’t know existed. The platform escalates unique risks to help prioritize the most critical vulnerabilities. Just knowing you have a vulnerability is not enough, Sonrai will help you understand the full scope of consequences, or the blast radius, for each unique potential risk – that is invaluable information for a business juggling priorities.
Where there are gaps in the cloud, Sonrai can fill those too. This elevates your vulnerability management further than just scanning and discovery. Risk Amplifiers provide additional host-specific identity, platform and data issues through our Toxic Permission Analyzer and Cloud Access Intelligence.
With Sonrai, you can meet all your security needs in one integrated product. Our workload security solution fits in seamlessly with our identity graphing technologies, continuous misconfiguration detection and automation and intelligent workflows.




