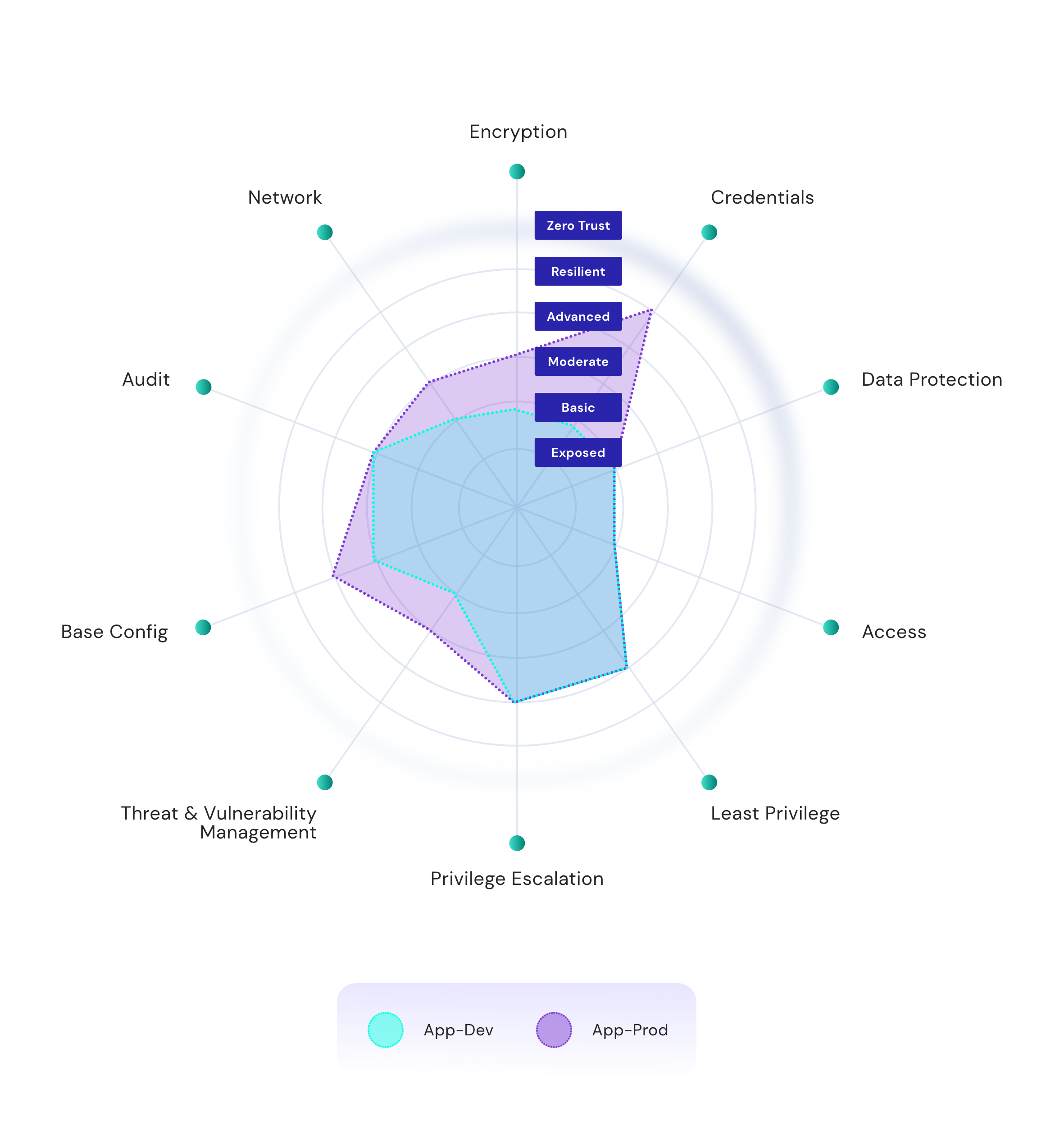
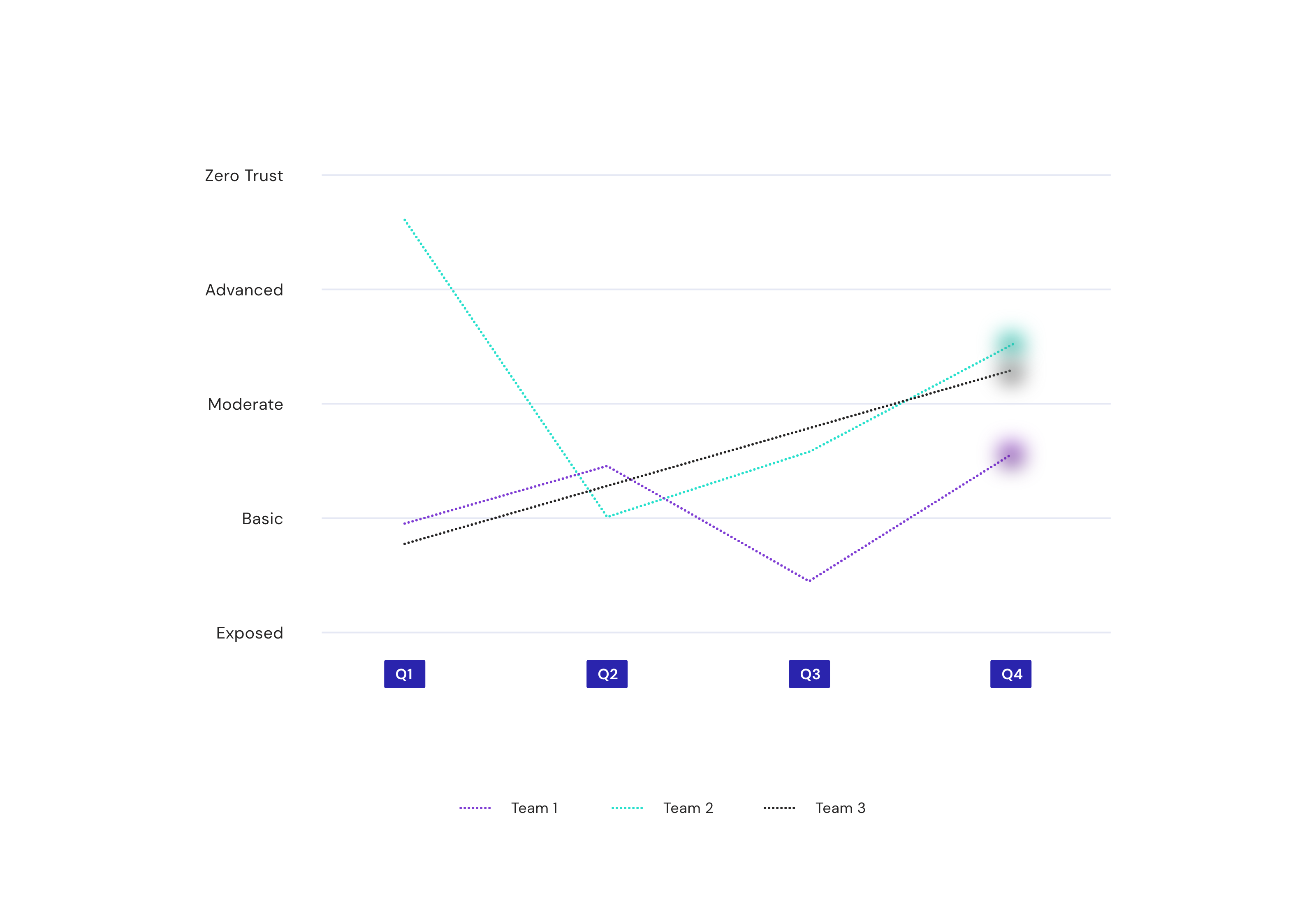
Executive Reporting
Get everyone to buy in on cloud security operational success
“Tickets closed” doesn’t cut it. Use real metrics they can understand.
Security will be a board-level imperative when executives can grasp what’s happening in the cloud in language they understand. Show how teams or departments are progressing towards goals, track & justify your long term strategy, and demonstrate the business impact of securing the cloud.