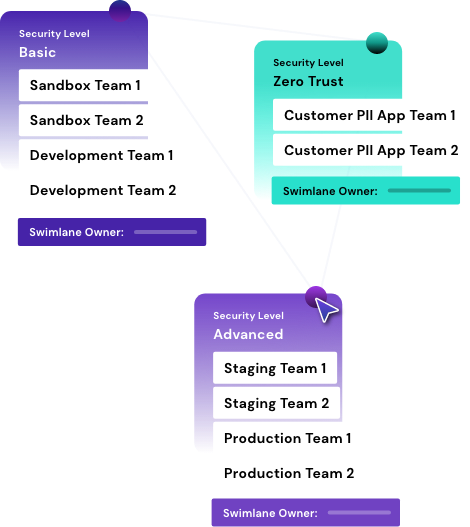
Cloud Teams:
Operationalize cloud security
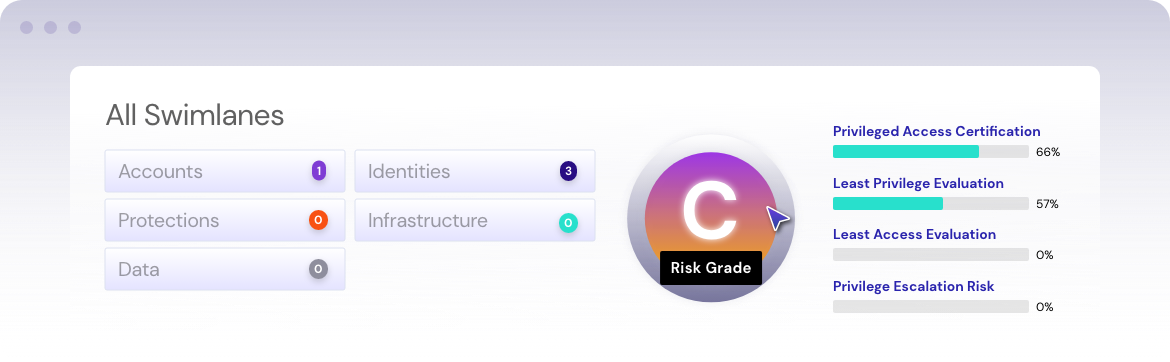
Set goals. Track progress. Operationalize cloud security at scale
The promise of the cloud is alluring to businesses — make everything faster, more dynamic, more future-proof
This pushes cloud teams for fast and efficient cloud utilization towards a grand digital transformation goal, leading to a “build first, organize later” philosophy that doesn’t allow for operational sustainability. Unless the cloud team can embrace a strategy with tools that automate scaling and collaboration, it can lead to a misalignment of security, development, and cloud goals.