


Discover how each public cloud provider’s cyber security stacks up, and how enterprises are solving current threats to identity and data access with CSPM and identity tools beyond posture management.
Download our FREE Definitive Guide to Learn:
- Pros and Cons for AWS, Azure, and Google Cloud’s Identity and Access Management Mechanisms
- Review Differences in Security Practices Between The 3 Major Cloud Providers
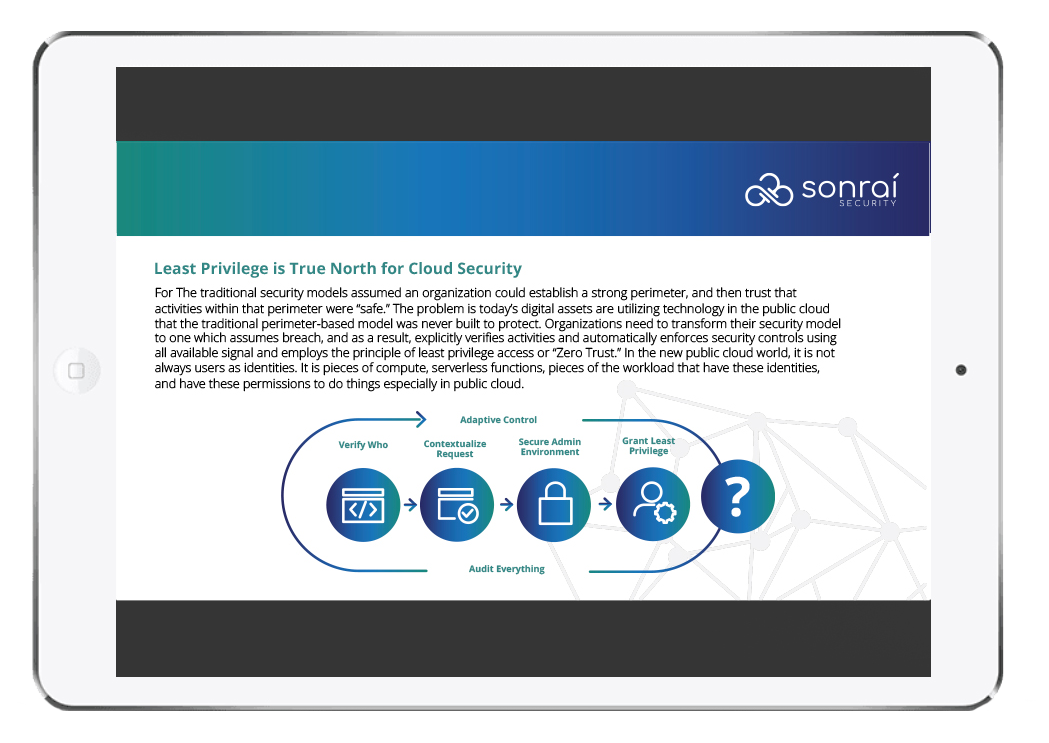
- Gain Insight Into Least Privilege as the Default Organizing Principle for Cloud Security
- How IT Security & DevSecOps Teams can Explain How The Shift to Public Cloud is Changing the Rules for Security
- What Principles Each Public Cloud Vendor is Using
- Different Approaches to Account Organization & How Resources are Protected.
FREE Definitive Guide to CSPM & Public Cloud Security
2019 SINET 16 INNOVATOR AWARD WINNER
Innovator award winner, Sonrai’s public cloud security platform provides a complete risk model of all identity and data relationships, including activity and movement across cloud accounts, cloud providers, and 3rd party data stores.

