WALLy finally puts you in control of cloud privilege. It finds risky permissions, fixes them automatically, and keeps developers and workloads running without interruption.
Trusted by Cloud-First Organizations Securing Privileged Access
Automatically Fix Risky Privileges with Policy-Based Controls
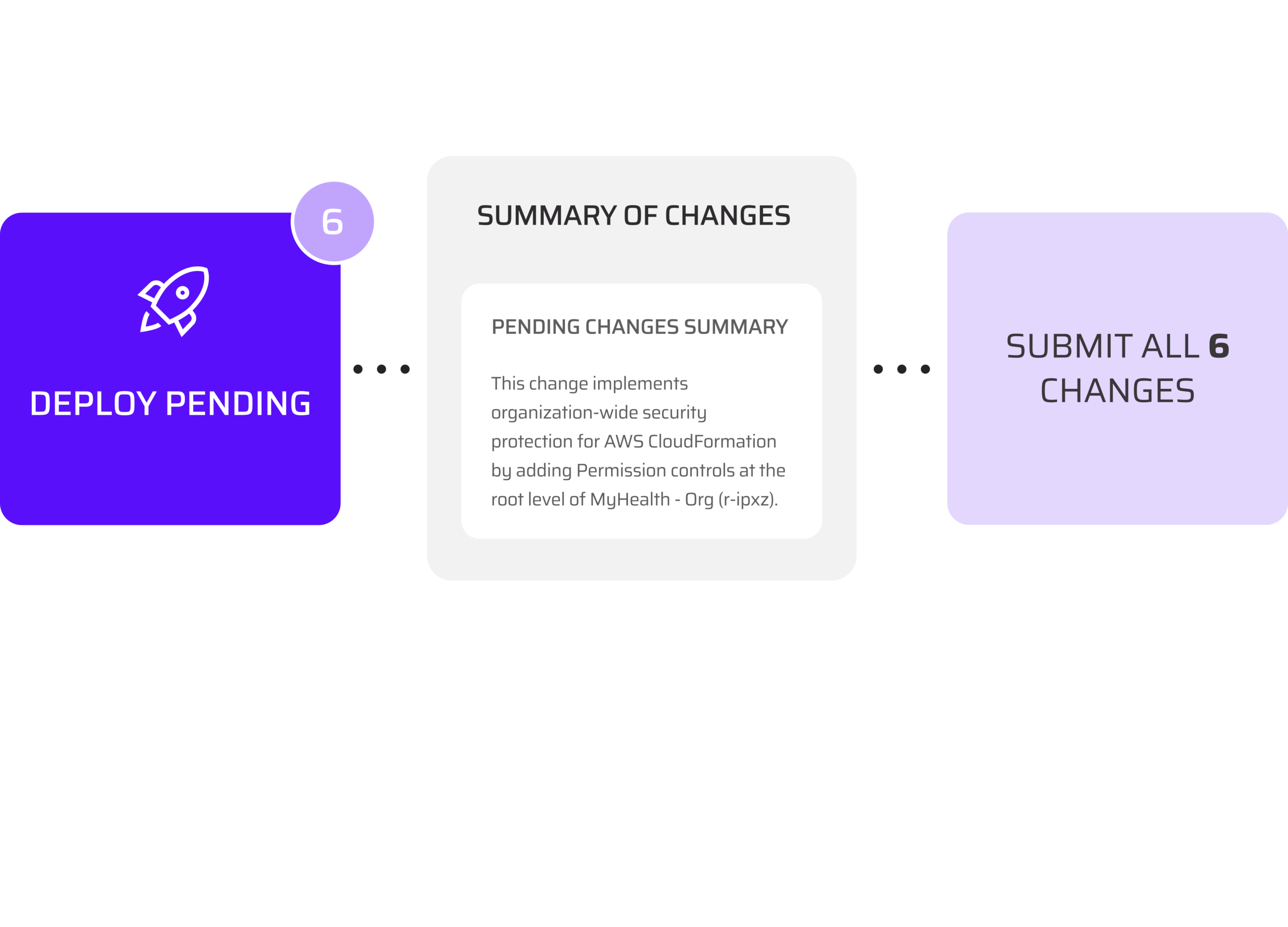
WALLy doesn’t stop at visibility. It builds policies to quarantine zombie identities, block third-party access, enforce just-in-time access, and remove dangerous cloud privileges. Every change is reviewed and approved by you before deployment.
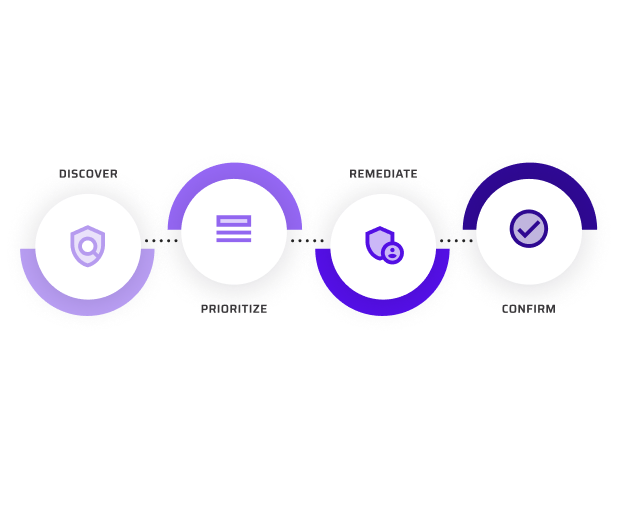
How AI Fixes Privilege Risk in the Cloud
WALLy scans your cloud environment and flags identities carrying privilege risk – overpermissioned roles, external accounts with IAM access, and identities with unused permissions tied to known attack patterns. It then ranks those findings by impact, so your team addresses the fixes that cut the most risk first.
From there, WALLy writes the remediation policies and stages them in the Cloud Permissions Firewall. A human reviews and approves before anything is deployed in your cloud. Once protections are live, WALLy confirms the risk has been closed.
No manual policy writing. No guesswork on where to start.
The Real Impact of Privileged Access Risk
80%+
of cloud breaches involve excessive or misused privileges
92%
of privileged permissions are
never used
61%
of identities are
unused
Guardrails That Protect Without Disruption
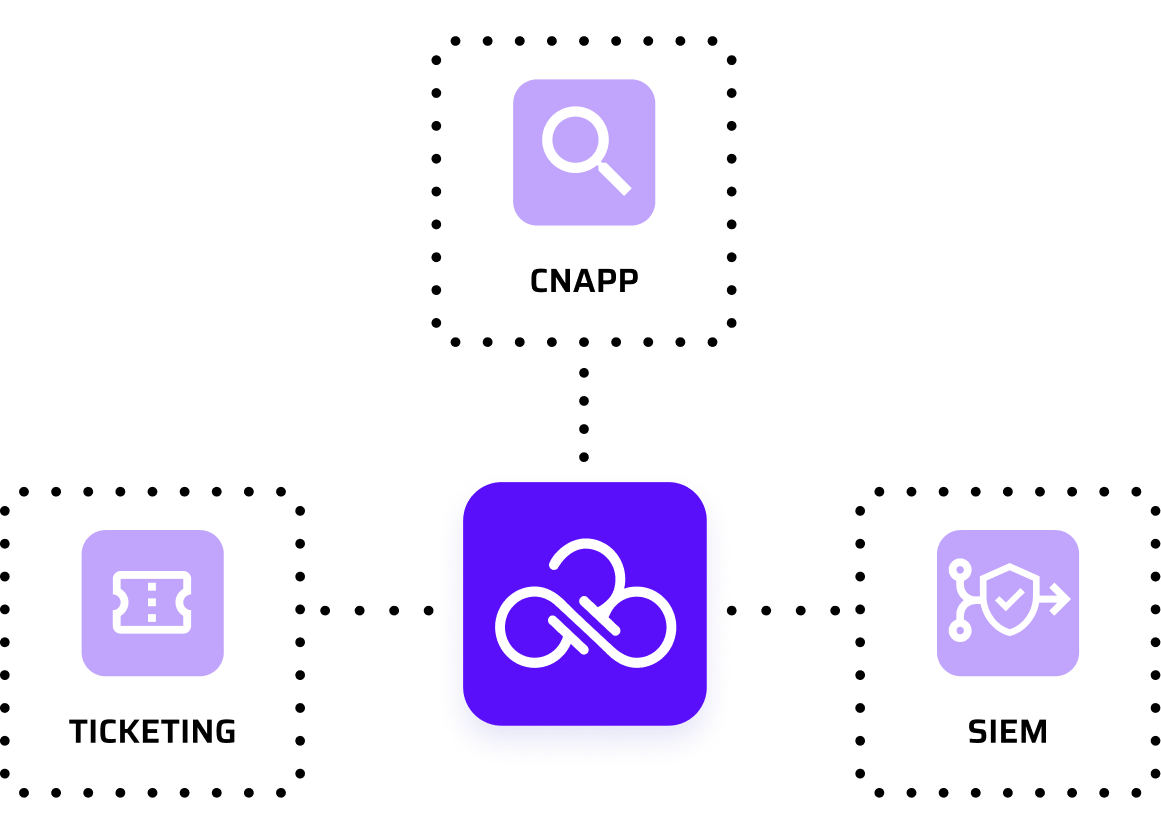
WALLy is built to fix cloud privilege risk without disrupting your environment. Every change operates inside Sonrai’s Cloud Permissions Firewall across AWS and GCP, enforcing role-based access controls (RBAC), detailed change history, and exception handling. You stay in control by reviewing and approving actions that reduce risk while keeping developers and workloads running without interruption.