Eliminate standing privileges with time-limited, approval-based access across cloud environments, strengthening cloud security without disrupting operations.
Trusted by Cloud-First Security Teams
Enforce Zero Standing Privileges with Just-in-Time Access
Remove persistent access for human users across sensitive cloud environments. On-call and break-glass accounts receive fast, secure, time-limited access through automated workflows or pre-approvals—ensuring security without disrupting operations.
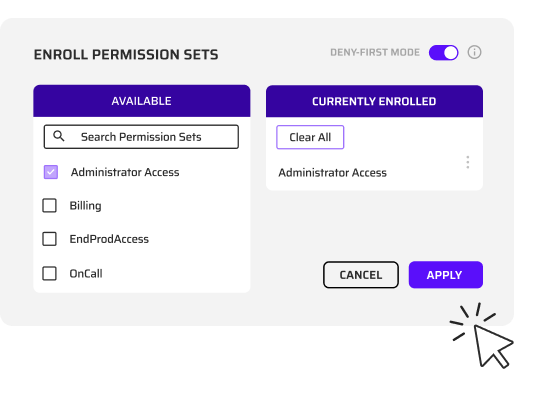
Granular JIT Access Control at Cloud Scale
Easily enforce just-in-time access across your cloud at any level—organization, OU, or account in AWS, GCP, or Azure. With one click, apply JIT to any or all permission sets using cloud-native technology. New permission sets are automatically enrolled, ensuring continuous security without manual effort.
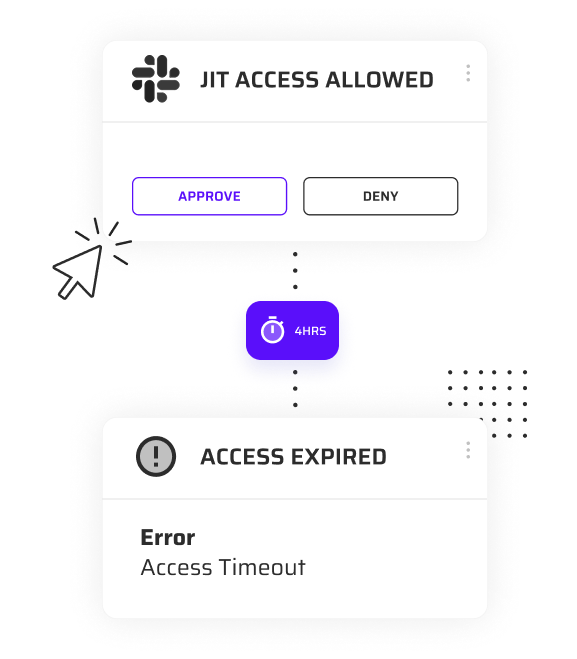
Automated Access Approvals
Users request access without logging into Sonrai – JIT automates approval workflows via ChatOps (Slack, Teams, Email), ensuring quick, secure access. Once granted, access is immediate and expires automatically, eliminating standing privileges without disrupting productivity.
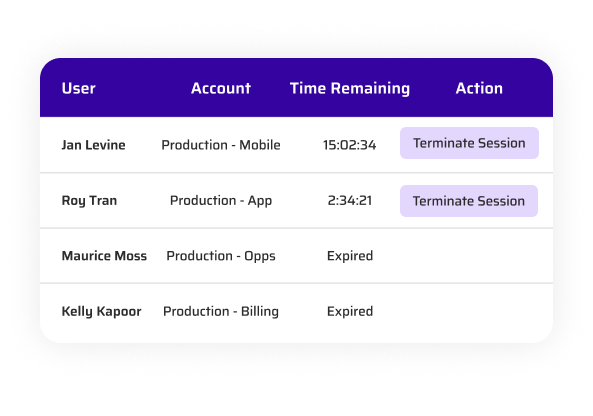
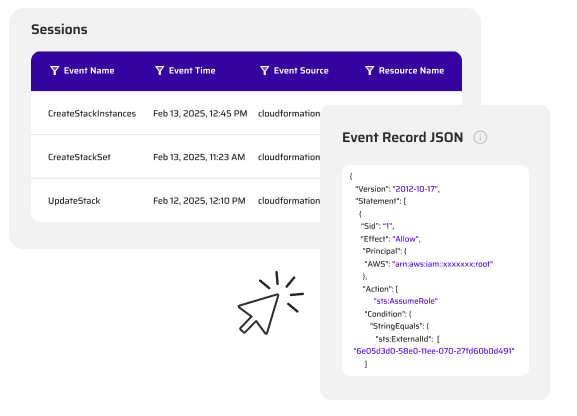
Revoke Access Instantly, Track Every Action
Administrators can terminate any active JIT session immediately, ensuring instant response to changing risks. Every session is logged with detailed activity summaries for audit and compliance tracking, ensuring complete oversight of privileged access in your cloud.
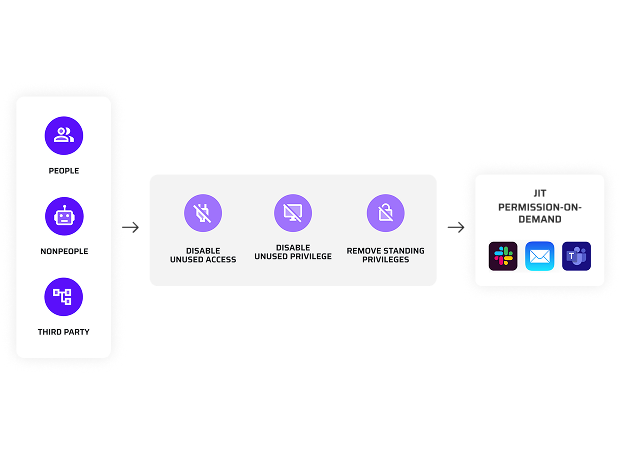
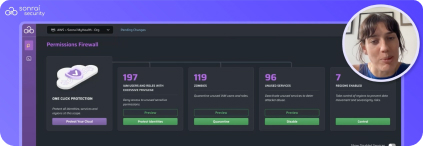
Part of a Complete Cloud Access Solution
JIT enhances the Cloud Permissions Firewall by ensuring secure, time-limited access to critical production environments. It works seamlessly with the platform, ensuring human, non-human, and third-party identities get access when they need it–nothing more, nothing less.
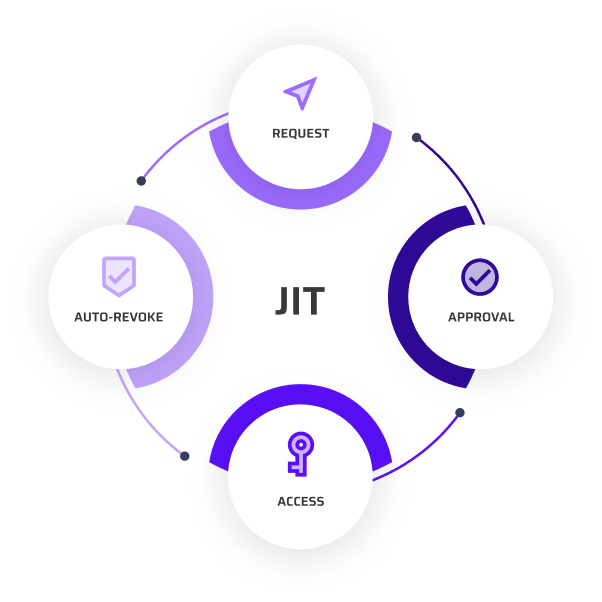
How Just-in-Time Access Works in the Cloud
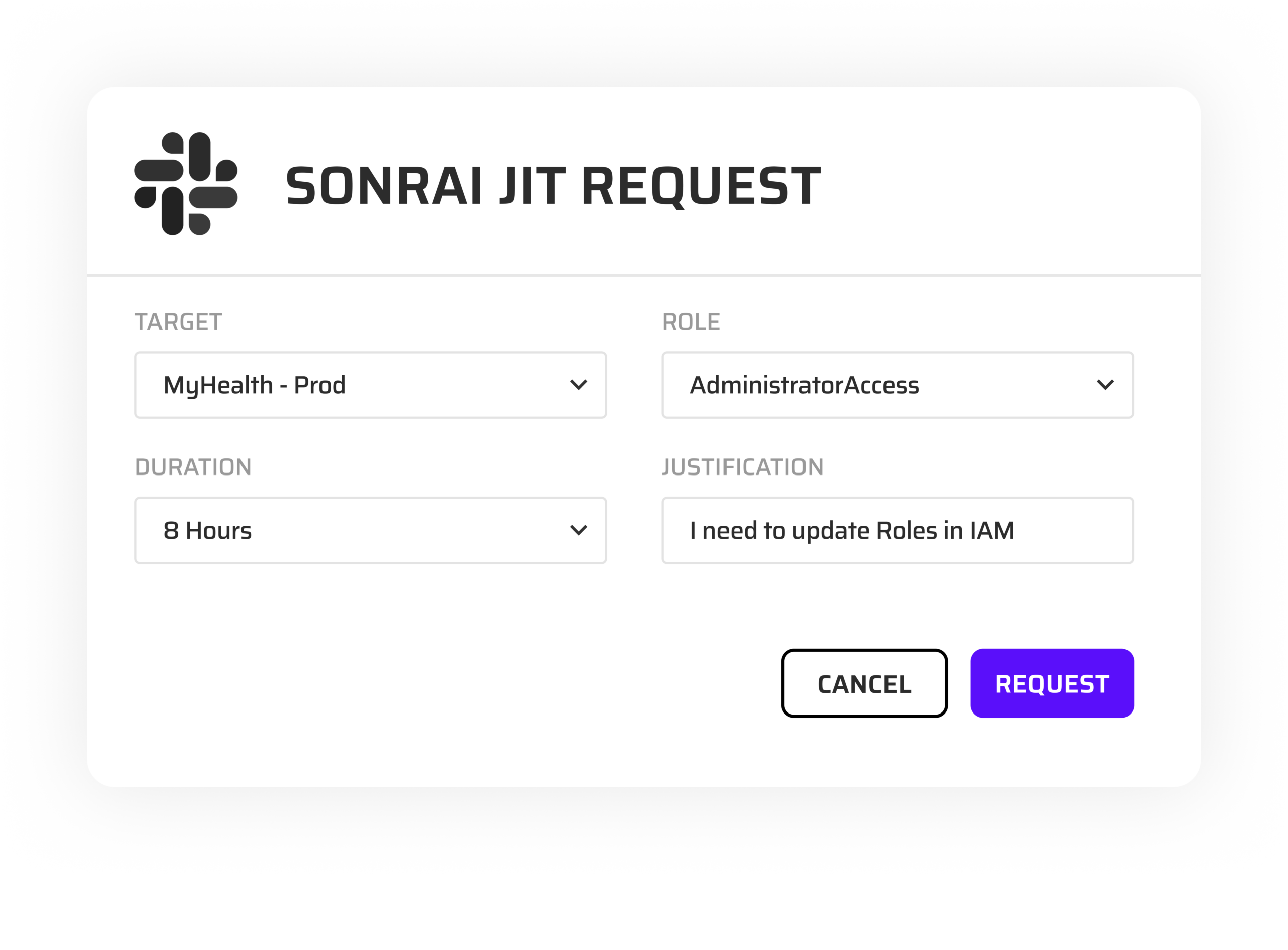
1. Request. When an identity needs elevated access, they initiate a request directly through Slack, Microsoft Teams, or email or by simply attempting access. The request includes the specific permission set needed, the duration, and a business justification.
2. Approval. Sonrai automatically routes the request to the appropriate owner. Approvers can review the context and grant access instantly.
3. Access. Once approved, the underlying cloud policy is updated in real time. The user receives immediate notification that their session is active and can begin their task.
4. Auto-Revoke At the end of the predefined time window, the Cloud Permissions Firewall automatically revokes the permissions. Standing access is eliminated, and a full audit trail and session summary is logged for compliance and security reviews.
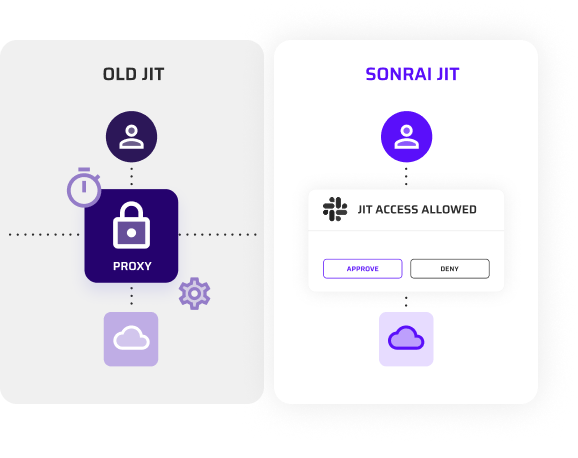
What Makes Sonrai Just-in-Time Access Different
Sonrai eliminates the need for jump boxes, bastion hosts, or connectors by enforcing access using native controls. One-click ChatOps workflows provide instant, time-limited access without the friction of legacy vaulting or manual tickets.
As a core component of the Cloud Permissions Firewall, this JIT capability works alongside automated enforcement to clean up unused privileges across your human and machine identities.
Integrates With Your Existing Cloud and Identity Stack
We believe granting required permissions on the fly should be easy. Request and approval processes live in the chat tools you already use today and all access changes are recorded in your ITSM.
Gain visibility and take the action you need in the tools you use today without the burden of a new process or UI.
The Real Impact of Privileged
Access Risk
80%+
of cloud breaches involve excessive or misused privileges
92%
of privileged permissions are
never used
61%
of identities are
unused
Trusted by Security Teams to
Reduce Privilege Risk


Cole Horsman
AVP, Security Operations“Sonrai helped us do in days what would’ve taken months—automating identity management and achieving least privilege across AWS.”

Preetam Sirur
Chief InformationSecurity Officer
“The challenge with deleting unused identities or enforcing least privilege is that we know it’s the ‘right’ thing to do, but everyone’s afraid it’ll break something or interrupt our development cycles. We don’t have to worry anymore.”


Brendan Putek
Director of DevOps“Within five minutes I had disabled regions that were unused across my entire AWS organization.”


Kenneth Milcetich
Director of Cyber and InfoSec“Sonrai not only identified the over permissive actions granted to our identities, but also provides a least effective access policy based on the identities usage...All of this boils down to a significant increase in our cloud security posture.”


Josh McLean
Chief Information Officer“Our transition from tedious, weeks-long tasks to accomplishing Least Privilege outcomes in just a few days has been remarkable. This approach has saved us a tremendous amount of time while also guaranteeing the security of all critical permissions.”


Chad Lorenc
Security Delivery Manager“Sonrai is one of the top tools to quickly scale when you're trying to do privileged management in the cloud.”

Just-in-Time Access Resources
Just-in-Time Access:
See it in Action
Curious about how just-in-time access works in your
cloud? Get a demo today.