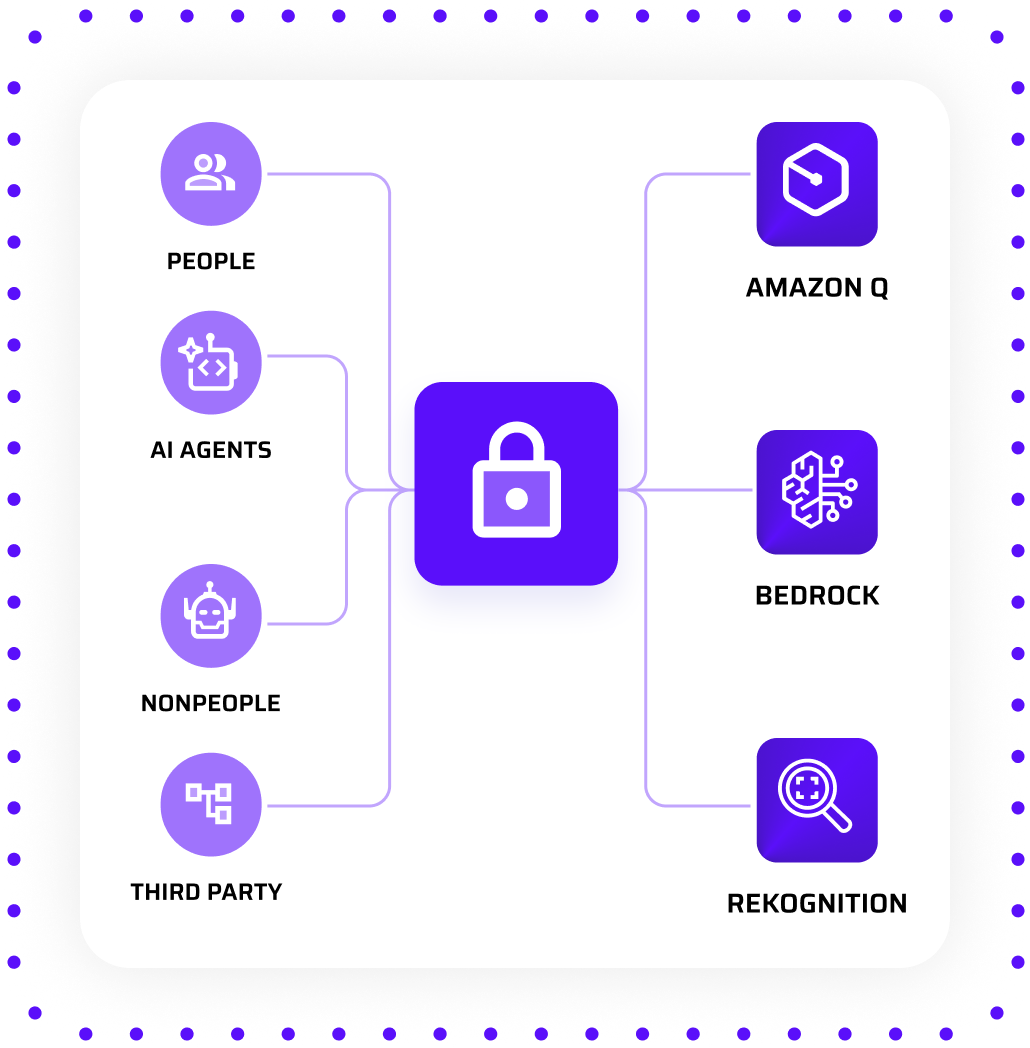
Secure AI agents, models, and AI services by controlling who can access them and what actions they can perform through identity-based policies.
Leading Cloud Organizations Rely on Sonrai
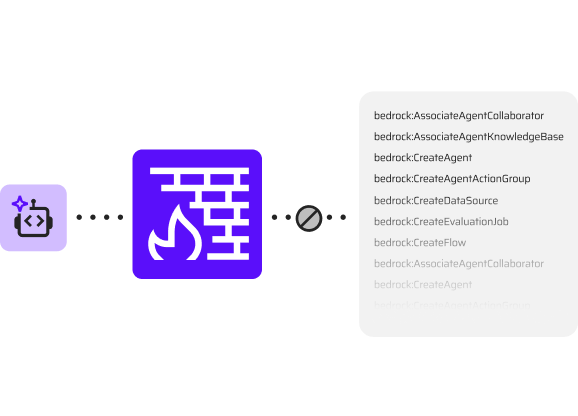
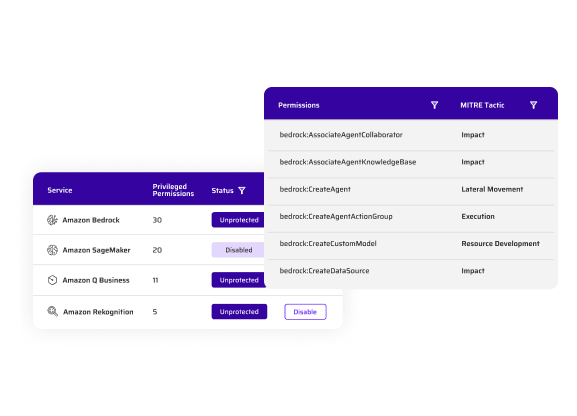
Stop AI Agents from Performing Actions They Shouldn’t
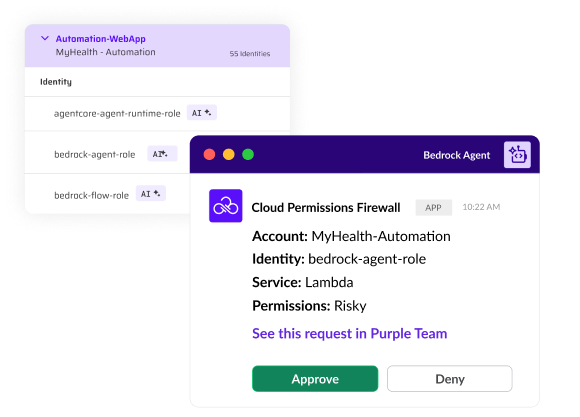
AI agents are identities, so treat them like it. They assume roles and inherit permissions just like any human user. Whether exploited by a bad actor or misused by a well intended employee, AI agents can take damaging action. Sonrai enforces permission boundaries at the IAM level, blocking agents from acting outside their authorized workflow while seamlessly granting access on demand when needed.
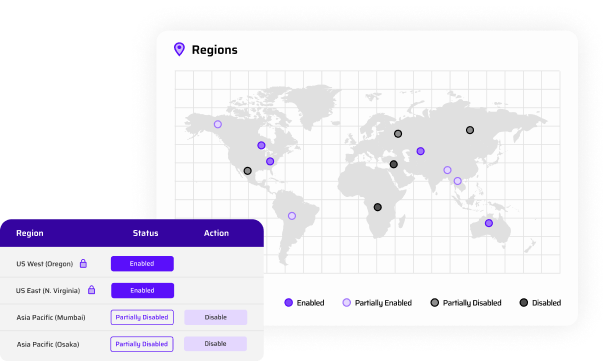
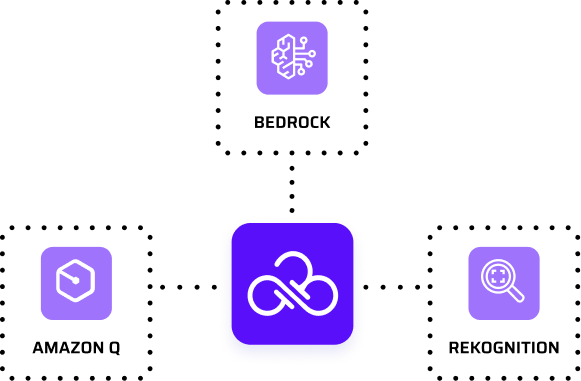
Prevent Unauthorized Access and Misuse of AI Services
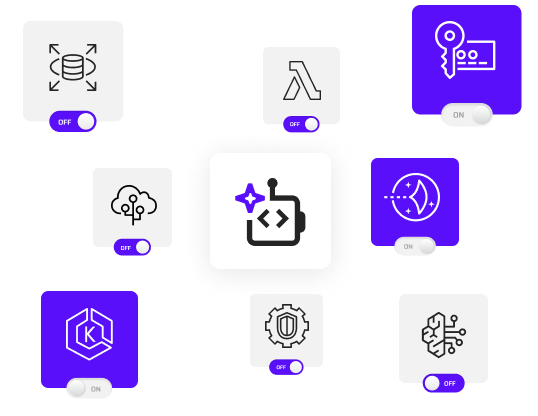
Not every team, account, or identity should have access to every AI service. Sonrai’s Cloud Permissions Firewall lets you restrict access by scope, org-wide, by account, or down to individual identities, so you can completely block who can invoke models or interact with AI services in the first place. Stop unauthorized use before it starts.
Just-in-Time Access Resources
Learn how Sonrai Security's automated IAM solution enforces default-deny guardrails to secure AI agent permissions in the cloud without disrupting DevOps..
Discover why IAM permissions, not just Bedrock guardrails, are the true security perimeter for AI workloads deployed in AWS.
Sonrai Security researchers uncover and responsibly disclose a vulnerability allowing long-lived Bedrock API keys to bypass AWS Service Control Policy enforcement, and how to prevent similar gaps.