Table of Contents

Share this entry

What is the Principle of Least Privilege?
The Principle of Least Privilege (POLP) is widely recognized as a security concept that enforces giving an identity (a person or machine identity) only the permissions that are essential to performing its intended function. If an identity does not need the permission, they should not possess it. It is implemented to minimize the cloud attack surface and protect data by mitigate the number of opportunities for exploitation via permissions.
The Importance of Maintaining Least Privilege
Today, identities and permissions are the stepping stones of the cloud, and what we consider to be ‘the perimeter.’ Privileged access control is finally getting the attention it deserves and many established organizations are highlighting the role privileged accounts play in cloud breaches.
In fact, Forrester estimates that 80% of security breaches involved privileged credentials. The heavy influence privilege plays in cloud breaches is further backed by IBM’s annual Cloud Threat Landscape Report:
“In 99% of pen testing engagements, X-Force Red was able to compromise client cloud environments through excess privileges and permissions on cloud identities.
IBM Cloud Threat Landscape 2022
In other words, 99% of cloud identities (person and non-person meaning, service accounts, compute, roles, etc.) were overprivileged. This result is consistent with our own research at Sonrai, finding only 3% of permissions granted to actually be used. Increased privilege, especially excessive privileges, is just an increased attack surface.
It is apparent privilege is weaponized by attackers on their pathways to business data and disruption. The answer is mitigating those opportunities as much as possible. Enforcing a least privilege access policy is one step you can take.
Four Reasons You Need Least Privilege
There are four main identity risks that Least Privilege addresses. These include the separation of duty, dormant identities, privilege escalation, and toxic combinations.
Separation of Duty
Separation of duties (SoD) is an internal control concept that involves the distribution of responsibilities and privileges among multiple users with the intention of preventing too much privilege for one entity. It is designed to ensure that identities (people and machine) don’t have conflicting responsibilities.
To illustrate this concept — SoD entails that the individual responsible for designing and implementing security must not be the same person as the person responsible for testing security, conducting security audits, or monitoring and reporting on security.
Dormant Identities
Dormant identities are characterized by a lack of activity for an established amount of time. These dormant identities can be understood as unused credentials, keys, serverless functions, compute and various entities lying around your environment. Unused identities seem harmless, but they are sitting ducks waiting to be exploited by attackers. It is best to remove any unnecessary infrastructure or identities.
Privilege Escalation
Privilege escalation occurs when a malicious attacker is able to alter their associated privileges or inherit other privilege, often resulting from an IAM misconfiguration. There are five types of privilege escalation defined by Sonrai Security: direct self escalation, indirect escalation, unintended escalation, confused deputy and the resource permission escalation.
Read about the five different types of privilege escalation here.

Toxic Combination
Toxic combinations are the result of overlapping privileges that create abilities passed what is intended for an identity. For example, a developer is in group A and group B. Independently, those groups allow appropriate privilege, but their overlap allows risky power.
Benefits of Least Privilege
- Eliminates Human Error: Enforcing an identity and access policy like Least Privilege takes away the need for human manual efforts that could lead to unintentional error. Less error means less risk.
- Reduces Attack Surface: Granting identities the least amount of privilege possible to do their job means less opportunity to exploit. When an attacker enters an environment, they are searching for identities with the right permissions assigned to execute their intended outcome. Least Privilege reduces that leeway for lateral movement or the opportunity to exploit a privileged user.
- Streamlines Compliance/Audits: Some compliance frameworks entail following a Least Privilege policy outright, or have regulations around access for privileged accounts. Implementing principle of least privilege makes proving compliance a smoother process.
Notable Privilege Breaches and Threats
Two examples of public breaches that violated least privilege principle:
SolarWinds: This breach hit the headlines in 2020 with widespread damage. The attackers deployed malware into SolarWinds’ Orion source code. Customers were vulnerable to the supply chain attack because of one fatal mistake: the Orion application needs unrestricted access, or, shared admin access, to work. This is inherently unaligned with the principle of least privilege, and allowed attackers unrestricted privilege access through the compromised Orion application.
Uber: An attacker used social engineering to compromise an employee’s Slack account, persuading them to hand over a password that allowed them access to Uber’s internal systems. Once in Uber’s environment, the bad actor was able to move throughout the tech stack, gaining unimaginable access. The bad actor gained access to the company’s internal network *.corp.uber.com. From Uber’s internal network, the attacker found PowerShell scripts, one of which contained credentials for an admin account from Uber’s Privileged Access Management (PAM) solution.
The PAM controls access to multiple systems, and having admin access means the attacker can give themselves complete access or extract secrets to all connected systems. Critically, Uber’s platform was compromised through the exposure of its admin credentials. In this case, no privilege escalation was needed, just a compromise of a single employee or endpoint, some simple reconnaissance, and admin credentials stored in a script on an internally open share.
How Does A Least Privilege Policy Work?
A Least Privilege policy works by limiting an identity or group’s scope of access to resources, applications, data, and overall function. It helps designate identities into clear cut workflows or tasks, as opposed to giving identities the ability to do or perform anything they want.
An enterprise implements a policy to enforce least privilege and ideally regularly audits privilege usage to better understand what is needed and what isn’t. Leveraging a cloud security tool like a CIEM is a great way to uphold least privilege because it will automatically remediate policies that are in violation by suggesting alternatives in accordance.
Steps to Implement Least Privilege
- Gaining visibility into identities permissions across all of your public cloud infrastructures.
- Monitoring for permission usage, access requests, and what resources are accessed.
- Removing unused identities and unnecessary permissions from identities that go untouched for 30-60-90 days.
- Identifying permissions that identities only need for short periods and implementing automated processes to grant and remove these permissions.
- Implementing on-demand processes to speed up permissions evaluation.
- Investigating anomalous activity, particularly unusual usage or attempted usage of privileges, complete with automated remediation.
Best Practices to Maintain Least Privilege
Know Your Effective Permissions
This is a core pain point for many organizations – a lack of visibility into their cloud. Effective permissions are the logical intersection of compounding permissions, policies, and conditional access for any given identity. What is the true picture of what each and every identity can do in your cloud?
Understanding all the effective permissions of an individual identity is a problem that cannot be solved by evaluating a single policy or calling an API. Trust relationships, nested groups and other covert compounding privileges create a lot of complexity. The scale and scope of cloud leaves manual efforts insufficient – leveraging a cloud security platform is largely the only way to gain visibility into effective permissions.
Relentless and Continuous Monitoring
This relates to the monitoring of both data and identity. This starts with having a continuous inventory of all identities in your environment and data. Where is all your data? What is it? Who and what can and is accessing it? Critical resource monitoring is a must. Think of your most sensitive assets on lockdown with tripwires around them alerting you anytime someone breaches the barrier. Establishing these knowns then allows you to monitor your environment against secure baselines and detect deviations or suspicious activity.
Enable Your Teams to be Part of the Solution
First, educate your teams on least privilege principle best practices. Second, your organization should shift left by integrating your Security, Cloud, Audit, IAM, and DevOps teams. Security is no longer a security team issue – it is an organization-wide concern. Culturally, involving all aspects of your organization improves security by building security into your processes from the start, as opposed to last minute security checks.
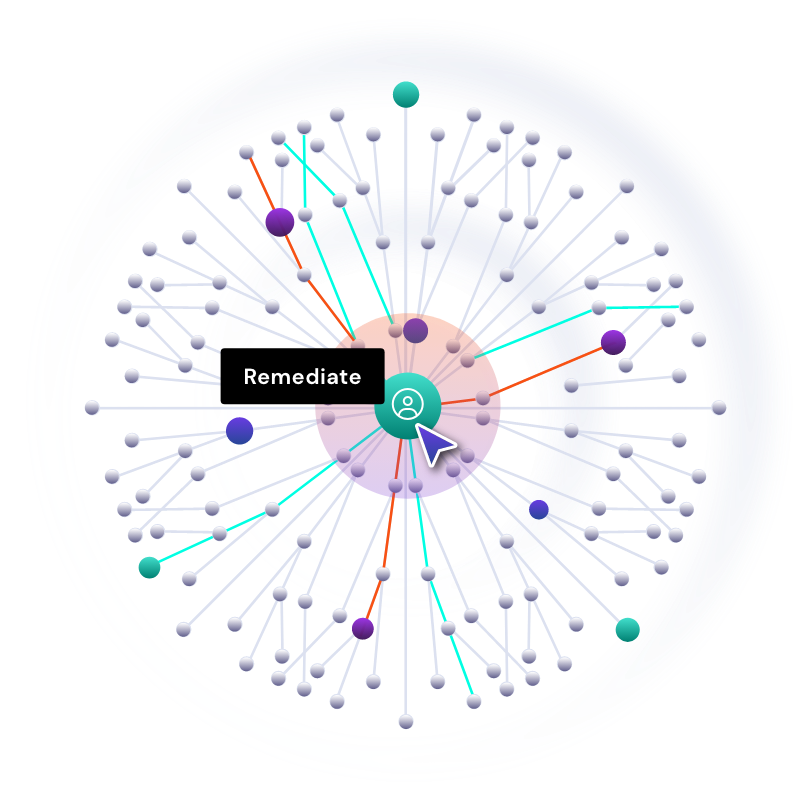
If There is an Issue, Fix it Fast
Operationalize your security processes. First line of security is preventing the problem from happening in the first place, but if you missed it, closing the gap quickly. Put prevention rules like policies or bot checks in place across your cloud and make sure they stay there. When issues are detected, you want a threat triaging process that alerts responsible parties quickly and efficiently.
Instant Least Privilege, Zero Disruption
What if we told you there was a better — easier — way to do least privilege? One without manual inventories, individually built policies, testing, and slow approval processes.
Sonrai’s Cloud Permission Firewall is the first solution to deliver sweeping least privilege that doesn’t strip developers of what they need to build quickly… in under 5 days.
The Cloud Permissions Firewall monitors for what sensitive access your identities need, builds a global policy you deploy restricting everything that is unused, and then maintains this state with a default deny and permissions-on-demand workflow for new access needs.

FAQs
Cloud Service Providers (CSPs) like AWS, Azure, and GCP offer various tools and services to support the implementation of the least privilege principle. They provide identity and access management (IAM) solutions that allow for granular permissions, enabling organizations to assign the minimum level of access necessary for users, applications, and systems to perform their tasks.
Organizations often encounter challenges when transitioning to a least privilege model, such as identifying the specific access requirements for different roles and managing the complexity of permissions across diverse systems and environments. The process requires thorough planning, continuous monitoring, and regular audits to ensure access controls remain appropriate over time.
The principle of least privilege can be applied across different cloud architectures, including Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS). The strategies for implementation may vary depending on the architecture type, with IaaS requiring more detailed configuration of network and server access controls, PaaS focusing on application-level permissions, and SaaS involving the management of user access to cloud-based applications.
THE ARCHITECT
The Newsletter for Cloud Security Leaders. 1x a month.
Read the latest news and insights
Sonrai cloud security platform, products and services are covered by U.S. Patent Nos. 10,728,307 and 11,134,085, together with other domestic and international patents pending. All rights reserved.